Apple started shipping special research iPhone hardware to security experts in 2020. Naturally, security researchers have been mostly coy about sharing the specifics of what Apple calls “rooted” hardware. Still, there are some program participants who grant a peek behind the curtains from time to time.
Lorenzo Franceschi-Bicchierai, writing for TechCrunch, provides context around one such researcher who shared photos of the instructions and sticker swag that comes with the Security Research Device:
lockquote class=”wp-block-quote”>
As for these days, Apple appears to have embraced the term jailbreaking by using it in the official instructions of the Security Research Device, according to a picture posted on X (previously Twitter) by security researcher Gergely Kalman.
“We’ve made it simple to get your existing tooling running on the Security Research Device. Through the cryptex subsystem, you can side load your tooling and it will run with platform privilege and any entitlement you’d like,” the instructions read. “This allows the rest of the security policies to remain enabled, providing the flexibility of a jailbroken device, while keeping the systems you’re investigating intact in a customer-like state.”
lockquote>
This is the X post shared this week:
Lorenzo Franceschi-Bicchierai goes on to write that Apple declined to say how many of these devices exist or if the program has resulted in a higher number of security holes being reported. However, Kalman provided a bit more additional info to TechCrunch:
lockquote class=”wp-block-quote”>
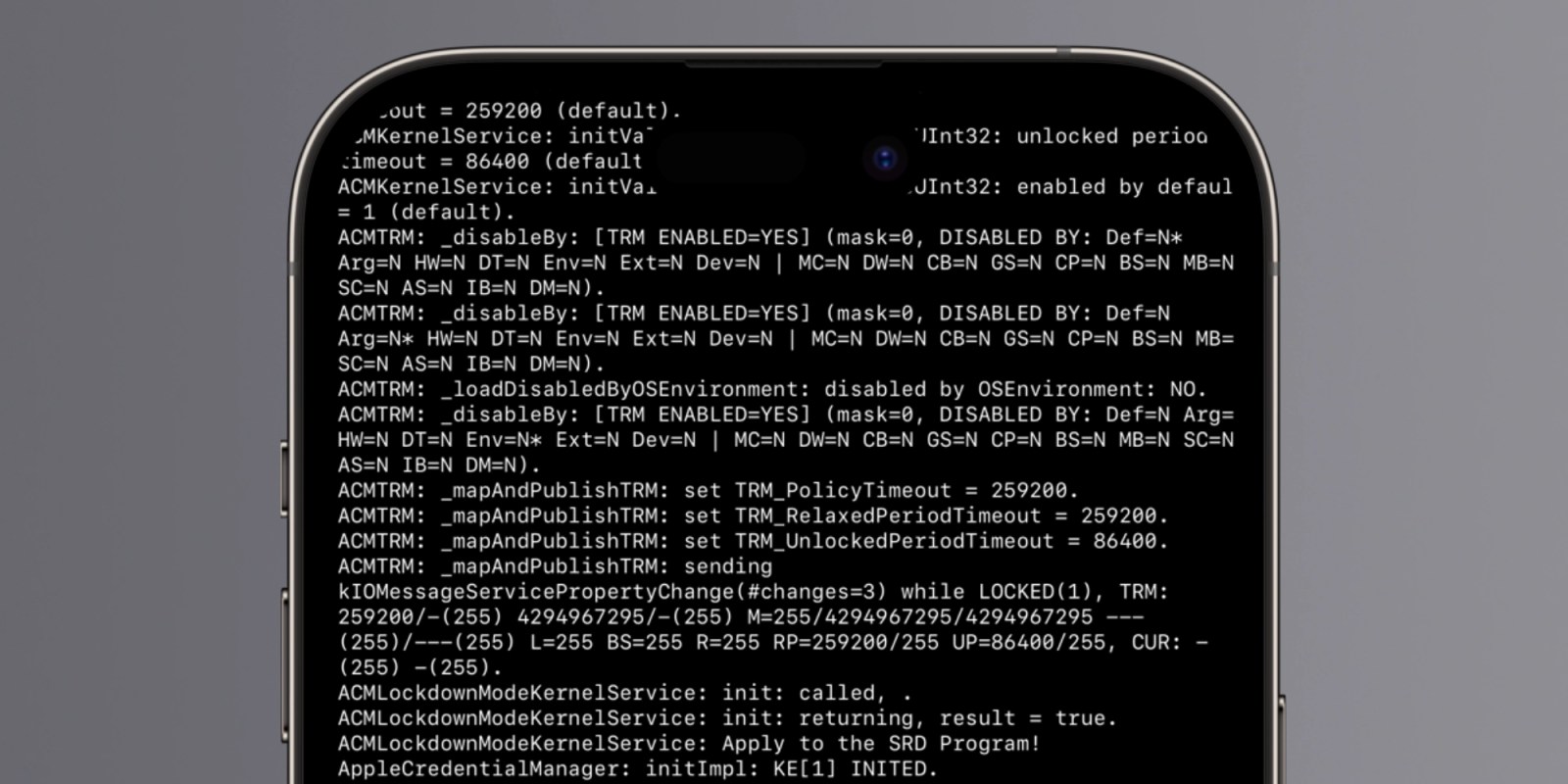
Kalman told TechCrunch that his Security Research Device is “identical” to an iPhone 14 Pro. The only difference, he added, is that at the bottom of the locked screen there is the writing “Security Research Device” and an Apple phone number, presumably to report it if it gets lost.
Apart from that, Kalman said there’s a special tag on the box that says “Do not remove” and “Property of Apple Inc,” along with a serial number, which Apple notes on its website. Kalman said there is also a marking on the side of the phone which says: “Property of Apple. Confidential and Proprietary. Call +1 877 595 1125.”
lockquote>
Perhaps even more interesting? This particular blog post that mostly when unnoticed before TC highlighted it today. Want to join on the bug hunting fun? Apple accepts researchers who have “a proven track record of success in finding security issues on Apple platforms, or other modern operating systems and platforms.” Learn more here.
FTC: We use income earning auto affiliate links. More.


![[CITYPNG.COM]White Google Play PlayStore Logo – 1500×1500](https://startupnews.fyi/wp-content/uploads/2025/08/CITYPNG.COMWhite-Google-Play-PlayStore-Logo-1500x1500-1-630x630.png)